See the system. Ask it anything. That's explainable AI.
Knowledge and action live in the gap between dashboards.
Your data tools understand metrics. Your strategy tools manage goals. Nothing connects both. People change when they see the system, not the dashboard.
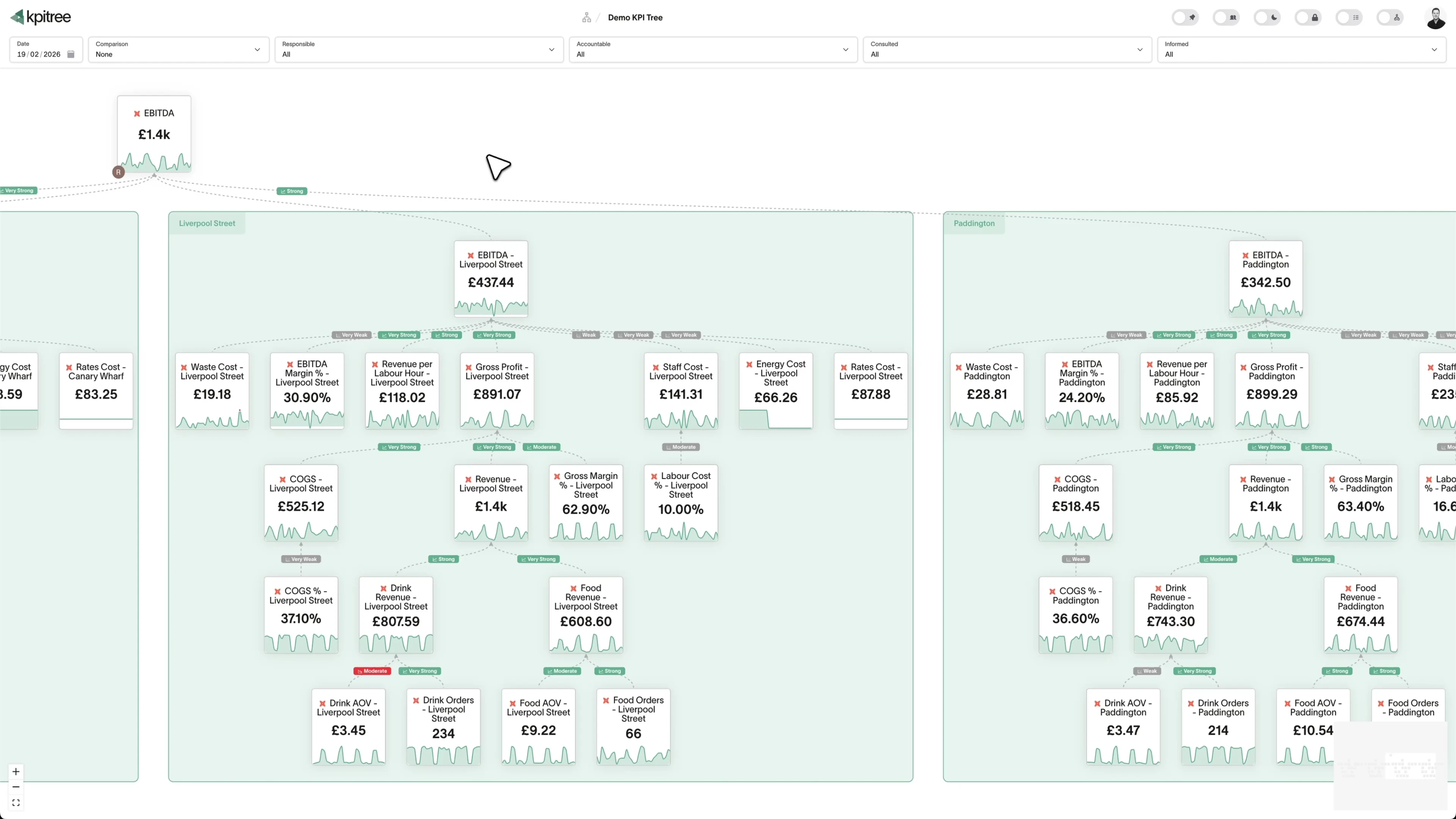
KPI Tree shows you why it happened, who owns it, and whether they moved the needle.
Purpose-built to close the loop from metric to action to verified impact.
See cause and effect across your entire business
Decompose your North Star into every lever your teams control. Every relationship has a direction and a measurable strength. The Five Whys, pre-answered.
Connect lead indicators to lag metrics, all the way up to your north star.
Metric tree. Map inputs to outcomes, visually.
Build the cause-and-effect model behind your business and make it visible to everyone. From lead indicators to your north star, every relationship is mapped and measurable.
Your brand. Board pack ready, always.
Upload your own fonts and customise every colour to match your brand guidelines. Light mode, dark mode, or fully bespoke. Straight from KPI Tree to the boardroom.
Comparison. Compare any period, any date.
Compare any metric period over period, from any date. Last week's leadership meeting, the day you built the board pack, end of Q3.
Granularity. Any time grain, zero modelling.
Switch between daily, weekly, monthly, quarterly, and yearly views instantly. KPI Tree aggregates automatically from your raw data.
Grid view. The spreadsheet your CFO already knows and loves.
A familiar rows-and-columns interface with built-in superpowers. Every metric shows its comparison period at every date going back to the beginning of time, and you can instantly aggregate to weekly, monthly, or quarterly with a single click.
Data quality. Confidence to act on every metric.
Every metric is continuously checked for outliers, gaps, and staleness so you know when to trust the data and when to dig deeper.
Correlation. Test what drives growth. Statistically.
Turn assumptions into evidence using AI correlation analysis, without hiring a data scientist.
Root cause. Why did it change? Answered.
When a metric moves, KPI Tree traces the full tree to surface contributing factors, ranked by impact and depth.
RACI. Every metric has a name on it.
Assign a RACI matrix to every metric so accountability scales with your business. Everyone knows what they own, who to escalate to, and who needs to be informed.
Tasks. Targets that track themselves.
Create metric goals with targets that auto-complete when hit, or assign simple tasks. Progress bars show how close each goal is in real time.
OKRs. Align the team on what matters.
Set objectives with measurable key results. Track progress toward each target automatically and see at a glance what's on track, at risk, or behind.
Subscriptions. Push insights to where your team works.
Deliver personalised actions via Slack, Email, WhatsApp, SMS and more. Every insight reaches the right person in the right channel.
Engagement heatmap. See who's acting on data.
Track engagement across teams and individuals. See who is viewing metrics, who is taking action, and who needs a nudge. CRM-grade analytics for your data culture.
API. Build on our engine.
Access precalculated correlations, comparison periods, metric relationships, and more via REST. Build custom dashboards, integrations, or workflows on top of our compute layer.
MCP. Context is everything.
Your semantic layer tells AI how metrics are calculated. KPI Tree adds the layer above: how they drive each other, who owns them, and what's being done about it. That's how AI goes from returning data to driving action.
Platform
Connect to your existing data stack in minutes, then let our proprietary compute layer handle the rest.
Your metrics. SQL or semantic layer, you choose.
Define metrics with SQL and connect directly to your warehouse. Already using dbt Cloud, dbt Core, or Looker? Sync your entire metric catalogue with prebuilt GitHub Actions.
Single pane. Every source, one tree.
Connect Snowflake, BigQuery, Databricks, Redshift, Azure SQL, and more simultaneously. Metrics from different warehouses sit side by side on a single tree. No stitching required.
1 query per metric. One.
Each metric runs a single query to sync raw data from your warehouse. Every aggregation, correlation, comparison period, and outlier detection after that runs in our encrypted, HSM-backed, proprietary in-memory compute engine. Instant results without increasing your warehouse bill.
Flat costs. Scale metrics, not your bill.
Your warehouse bill stays flat as you add metrics. All the heavy computation runs in our engine, so your costs scale with us, not with your data.
Enterprise
Built for Enterprise
Designed from the ground up to meet enterprise-grade security and compliance standards.
SOC 2 ® Type II.
SOC 2 Type II is considered the gold standard for compliance. Unlike point-in-time audits, Type II verifies that our controls operate effectively over an extended period. Independently examined for Security, Availability, and Confidentiality, our report demonstrates our sustained commitment to protecting your data with enterprise-grade controls.
SSO. One click, your identity provider.
Secure access through your identity provider. SAML 2.0 and OpenID Connect supported. Your team logs in with credentials they already have.
Directory sync. Users managed automatically.
Sync users directly from your corporate directory (Microsoft Entra ID, Okta, Google Workspace). Access is automatically managed as your team changes, with instant provisioning and deprovisioning.
Audit logs. Stream to your SIEM.
For highly regulated industries, stream user activity and security audit logs to your existing SIEM provider. Compatible with popular services like Datadog and Splunk for centralized security monitoring and compliance.
Endpoint protection. Restrict access to approved IPs.
Enhance security with endpoint protection services. If you use services like Zscaler, we can restrict login attempts to your approved IP ranges only, preventing unauthorized access from outside your secure network.
HSM encryption. Hardware-backed, always encrypted.
By design we do not store your data, it is fetched on the fly when needed. Any data that is temporarily cached is encrypted at rest using a Hardware Security Module (HSM).
BYOK. Bring your own key.
For customers in regulated industries you can bring your own key to encrypt your data at rest.